There are four labs that support courses with a strong cyber defense content. The names of these labs, their location, the courses that they serve, the available lab resources and sample student projects are listed below:
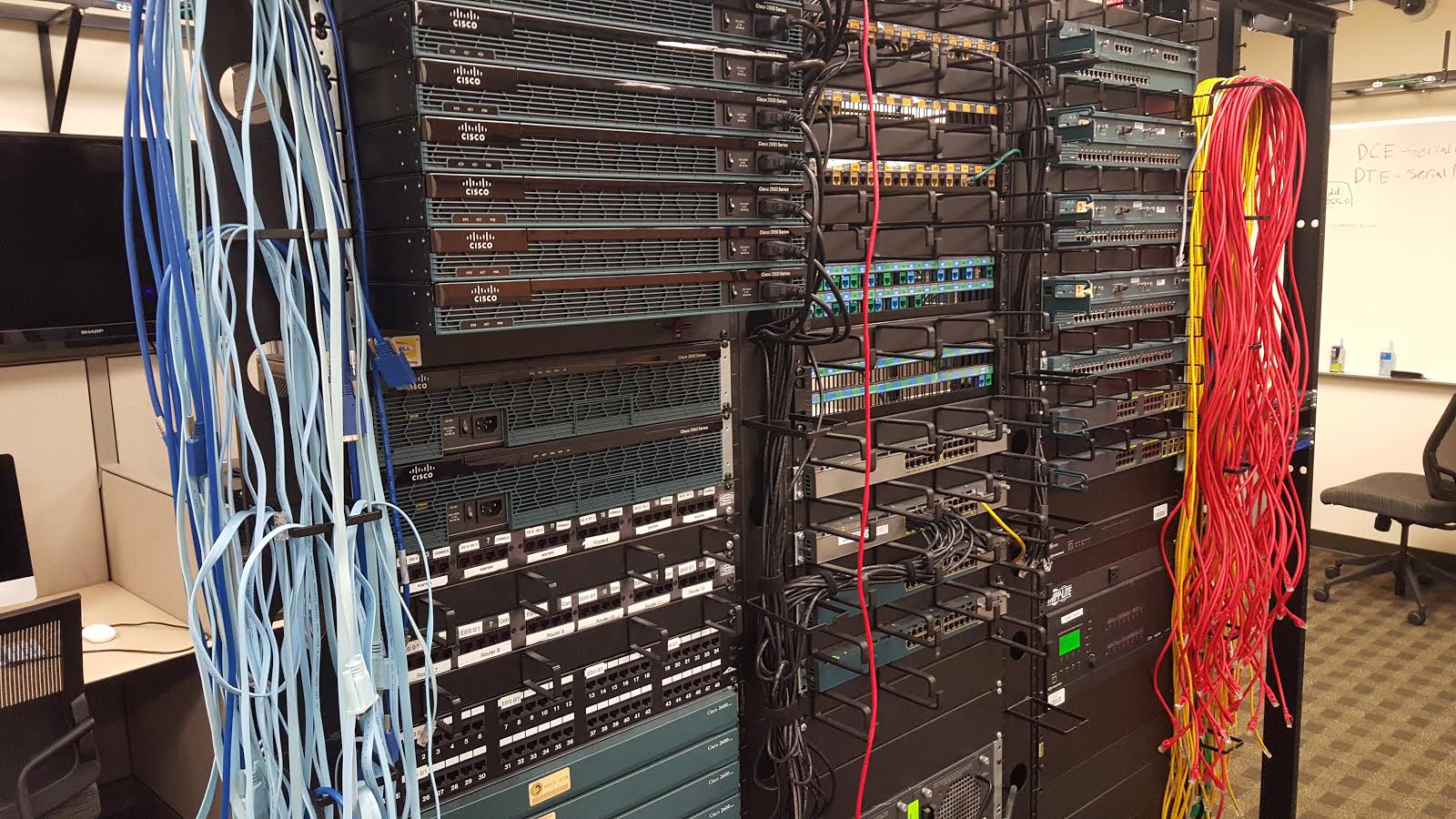 Lab Name: The Network Lab
Lab Name: The Network Lab
Lab Location: Harris Engineering Center, Room 322
Courses Supported by the Lab: The four courses supported by this lab are: CNT 4703 (Design and Implementation of Computer Communication Networks), CIS 4932C-ST: Topics in Cyber Security, CNT 4603- System Administration, CEN 4932C– Cloud Computing Administration.
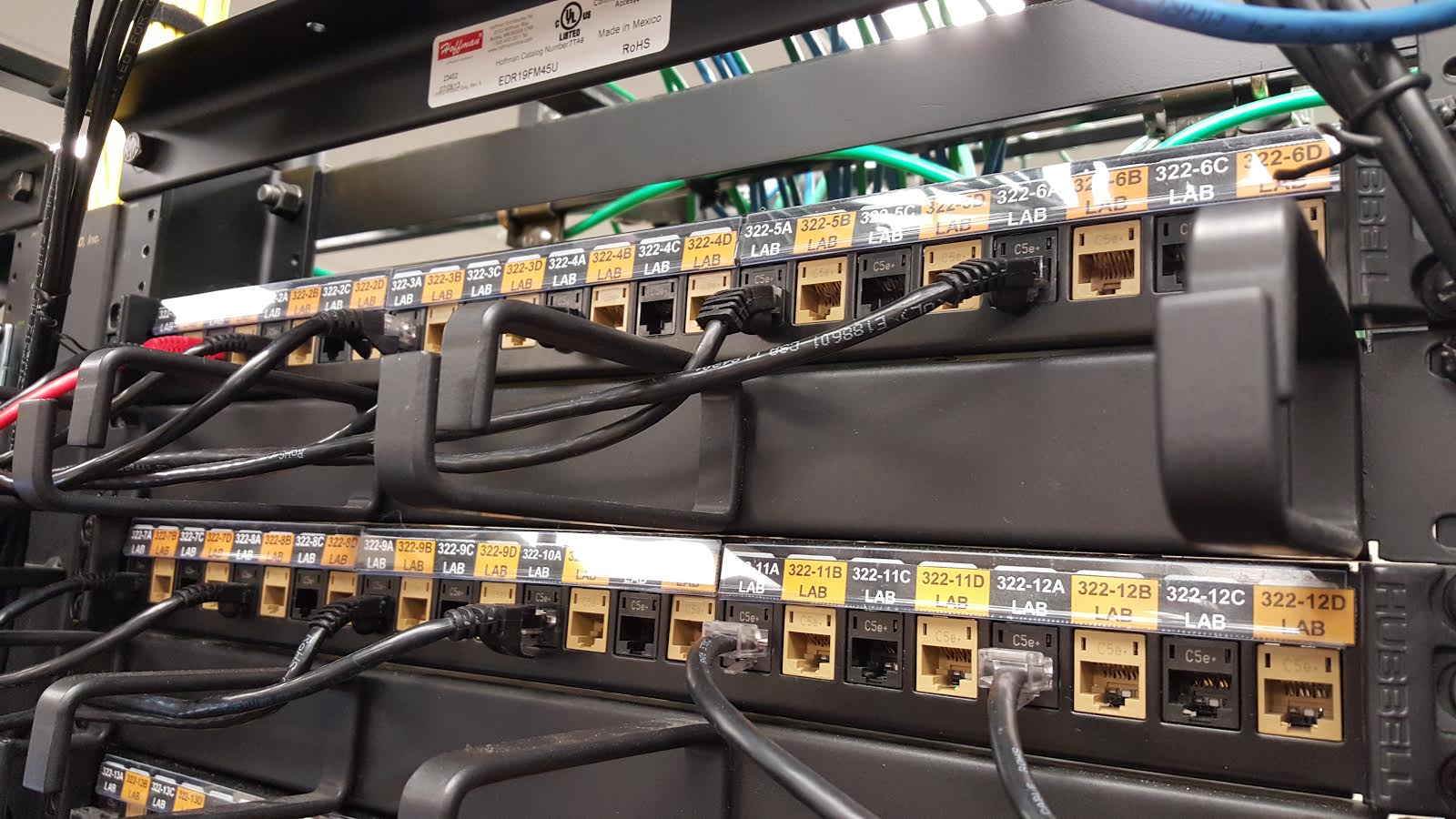
Lab Resources: Computers: 10 Dell Optiplex 9010 Desktops with Monitor, 3 Dell Optiplex 9020 Desktops with Monitors, 13 Apple iMac 21.5”; Servers: 2 Dell PowerEdge T110 II Servers, 1 Dell PowerEdge T620 Server with Monitor; Voice Over IP: Digium VoIP Phones; Networking Equipment: 1 Juniper EX2200 Switch, 1 Juniper SRX 240 Services Gateway, 1 Cisco Catalyst 2900 Switch, 4 Cisco Catalyst 2900 XL Switches, 2 Cisco Catalyst 2960G Switches, 1 Cisco Catalyst 4503-E Switch, 2 Cisco Catalyst 3560-X Switches, 2 Cisco Catalyst 3750-X Switches, 2 Cisco NCS 7800 Call Manager / Unity Voicemail Servers, 5 Cisco 2600 Routers, 12 Cisco 2900 Routers, 1 Cisco Wireless Access Point; Multimedia: Multimedia system with 6 37” Sharp TVs and Crestron Control Unit; Miscellaneous: 2 Liebert GXT3 UPS / Battery Backup Units, 4 19” Equipment Racks. All computers have sufficient storage, memory, and processing power to run one or more virtual machines so that students can gain exposure to various operating systems and or simulate client/server environments. Computers are also connected to a UPS at each station. In addition to the above networking equipment, the lab has several patch panels with 288 total ports. 
Samples of Lab Experiments: CNT 4703C: Students in the CNT 4703C class learn networking concepts and obtain hands-on experience in setting up their own networks. The Network Labs given in this course cover a wide range of topics including: cabling, using TCP/UDP in simple applications, VLANs, network addresses, redundant networks, routing, CISCO router and Catalyst switch configuration, and setting DNS servers. A few examples of projects in the CNT 4703 are listed below.
- Network Laboratory # 1: Lab Title: Cabling; Objectives: 1. Distinguishing between different kinds of cabling media and their usage; 2. Making straight through and crossover cable; 3. Usage of punching-down tool; 4. Usage of a cable tester to verify that a straight through or a crossover is good or bad; Equipment: Cables, Crimping tools, Punch-down tools, Cable cutter, Cable tester.
- Network Laboratory # 2: Lab Title: IP Configuration and Testing for Windows Workstations; Objective: Configure a Windows host for TCP/IP connections, including: setting the correct IP address, setting the correct subnet mask, and entering default routing information.
Other Lab Usage: Collegiate Cyber Defense Competition Team; The team uses the Network Lab for training to prepare for the annual regional and national competitions. The UCF Collegiate Cyber Defense Competition Team placed first at the 2014 and 2015 National Collegiate Cyber Defense Competition in San Antonio, Texas held in April 2014 and 2015.
Lab Name: Computer Engineering Senior Design Lab
Lab Location: Engineering I Building, Room 456
Courses Supported by the Lab: The two courses supported by this lab are: EEL 4914 (Senior Design I) and EEL 4915 (Senior Design II)
Lab Resources: 10 Stations, each equipped with: - Tektronix MSO 4034B Digital Mixed Signal Oscilloscope, 350 MHz, 4 Channel - Tektronix AFG 3022 Dual Channel Arbitrary Function Generator, 25 MHz - Tektronix DMM 4050 6 ½ Digit Precision Multimeter - Agilent E3630A Triple Output DC Power Supply - Dell Optiplex 960 Computer. The Lab provides a workspace with instrumentation, equipment, and software for students to design and build their senior design project including projects related to Cyber Defense Applications.
Samples of Lab Experiments: There are a number of senior design projects that focus on cyber defense applications. Two examples of such projects are listed below.
- Close to Home: The Close to Home project is, at its core, an effort to provide home users a way to not only monitor their house to ensure its security, but also control several aspects of the house to save on their monthly power bills, and to provide them with peace of mind. http://www.eecs.ucf.edu/seniordesign/fa2013sp2014/g23/
- The Mobile Aerial Surveillance System (MASS): The Mobile Aerial Surveillance System (MASS) is a large blimp which has a camera system attached to it to provide the user with a overview of their surrounding area. The potential for the system is to give the user the ability to fly overhead with the camera system and auto-detect any people in the area. If they want to keep surveillance on one person in the camera view, they will be able to start tracking that persons’ movement with a click of a button on the User Interface for the blimp system on a computer. http://www.eecs.ucf.edu/seniordesign/su2013fa2013/g06/
Lab Name: Computer Science Senior Design Lab
Lab Location: Harris Engineering Center, Room 102
Courses Supported by the Senior Design Lab: The two courses supported by this lab are: COP 4934 (Senior Design I) and COP 4935 (Senior Design II)
Lab Resources: Technology: 10 Samsung 40” LED Smart TVs; one mounted at each group station so that students can connect computers and laptops to it and present content to the group, 1 Samsung 55” LED Smart TV wall-mounted in 3-person seating area to present content to a larger group of people, 5 Dell computers with Intel i7-4785T 2.2GHz processors, 8GB RAM, and 500GB hard drive, 3 Dell computers with Intel i7-4770 3.7GHz processors, 16 GB RAM, 2TB hard drive, 2 Apple iMac 21.5” Late-2012 model: 1 with Intel Core i5 2.9GHz, 8GB RAM, 1TB Hard Drive, NVIDIA G4 650M graphics card, and 1 with Intel Core i7 3.1GHz, 16GB RAM, 1TB Hard Drive, NVIDIA G4 650M graphics card, 1 locking server rack E242296, APC Smart UPS RT3000 (for servers), 1 Computing Server (Dell PowerEdge R730): Configured for students to run compute-intensive tasks in their own virtual servers, 2 Intel Xeon E5-2650 2.3GHz processors, each with 10 cores, 128GB RAM, 2TB Hard Drive, 1 Storage Server (Dell PowerEdge R720xd): Configured for students to store data for their projects, and for us to archive old projects, 2 Intel Xeon E5-2620 2.1GHz 6 Core Processors, 4 3TB Hard Drives, 2 300GB Hard Drives, 64GB RAM, 1 Web Server (Dell PowerEdge R320): Configured for students to run web applications / present Senior Design projects, 1 Intel Xeon E5-2407 2.40GHz Processor with 4 Cores, 12GB RAM, 2 300GB Hard Drives; Miscellaneous: Electronic locks so that enrolled students can access the room 24 hours per day, 7 days per week to work on projects, 3 security cameras to record activity in the room
Samples of Lab Experiments: There are a number of senior design projects that focus on cyber defense applications. Two examples of such projects are listed below.
- IoT Devices Software Security Analysis (IDSSA): The goal of this project is to provide a thorough analysis of security vulnerabilities in the software associated with various Internet of Things (IoT) devices. Using a reverse engineering procedure crafted by the team, we analyze the Bluetooth Low Energy communication protocols behind the Nike+ Fueldband and Xiaomi Mi Band fitness bands and introduce modifications to the mobile companion apps in order to expose possible security holes. We also analyze security vulnerabilities in the Nest Thermostat in an effort to help automate the introduction of custom patches onto the device that are developed by the Security in Silicon Lab research team. Our aim is to bring to light any exploits that may help companies produce more secure versions of these devices in future product iterations. http://www.eecs.ucf.edu/cssd/spring15/idssa/
- Siemens Big Data Analysis: Every day, more articles of unstructured data populate the internet where they are left untouched. Much of it contains raw text, unlabeled and unclassified. Analyzing these enormous amounts of data can lead to making discoveries and trends amongst it. This information, when fully realized, can be utilized to find unknown relationships between the entities it contains, such as people, businesses, or other groups. Taking these unstructured documents, we use natural language processing and named entity recognition to identify entities of people, organizations, and locations, and recognize the connections which link them together. Implementing Latent Dirichlet Allocation (LDA), the similarity between documents is discovered. And together, the relevancy of documents and the similarities of the entities they share can shed light on connections previously undiscovered. http://www.eecs.ucf.edu/cssd/fall14/siemens/
Lab Name: Security in Silicon Lab
Lab Location: Harris Engineering Center
Courses Supported by the Lab: The course supported by this lab is: EEE 4346 (Hardware Security and Trusted Circuit Design)
Lab Resources: Leading hardware security/cybersecurity research and educational lab
Samples of Lab Experiments: Samples of labs covered in the course, during the Fall 2015 semester are listed below.
- Lab 1: Hardware Trojan Design in AES Crypto-System
- Lab 2: Hardware Security Primitive - PUF Designs
- Lab 3: Vulnerabilities of Computing Platforms
- Lab 4: Hardware Trojan Detection in FPGA Bit Files
Furthermore, student researchers working with their advisor Dr. Yier Jin in the Security in Silicon Lab have identified the security vulnerabilities on a Google Nest Learning Thermostat which was presented at Black Hat 2014. A demo for this is available on You Tube.
- Hacking into the Nest Thermostat (SSL@UCF): https://www.youtube.com/watch?v=7AnvTgAKa-g